The incident on record
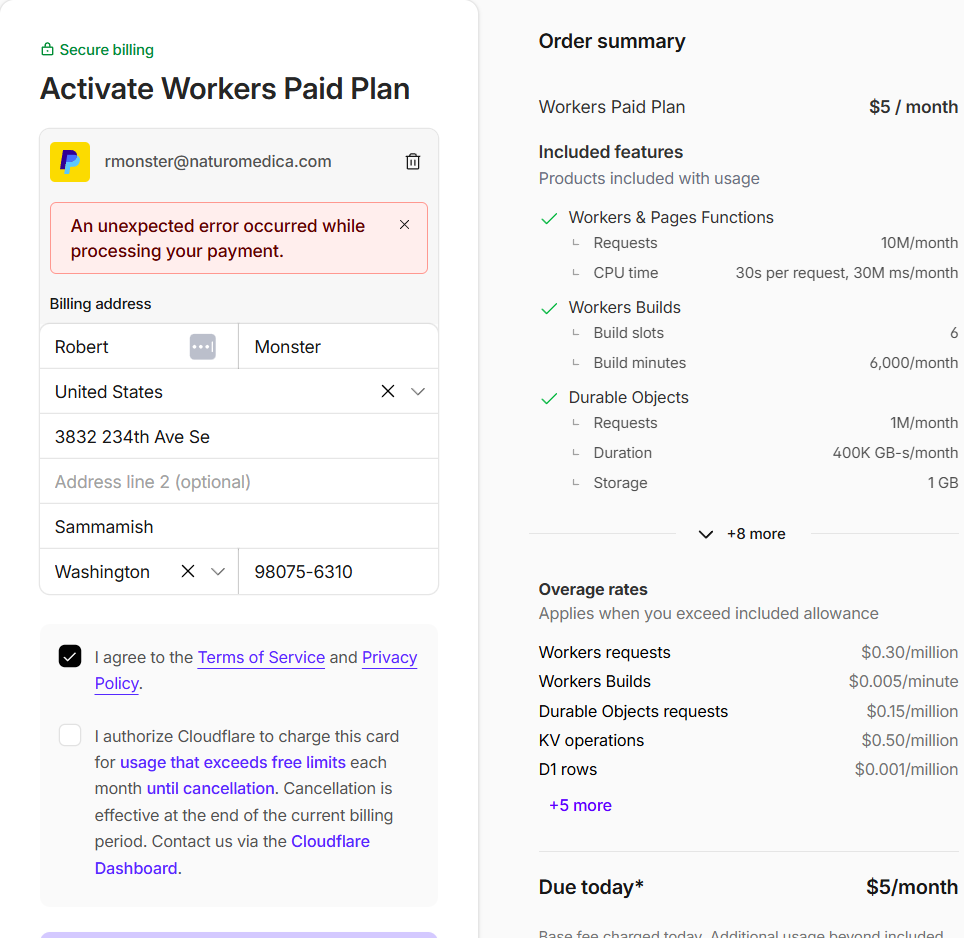
The payment paradox
Cloudflare blocked their own payment gateway across four separate payment methods while simultaneously enforcing limits that require payment to resolve. The customer is trapped in a loop with no exit path.
Selective notification
Cloudflare sent an automated email at 90% of limit. They sent nothing when they crossed 100% and terminated all traffic. A company that emails at 90% and goes silent at 100% is making a deliberate choice.
No due process
164 domains — representing a civic infrastructure network for greater Seattle — taken offline in a single automated action. No warning. No grace period. No appeal path. No human on record.
"A website is speech. It is not a bomb." — Matthew Prince, Cloudflare CEO, 2012 (on not taking down websites)